Incident Response
Readiness 2026
/reports
Ransomware lands at 3am. Who calls counsel. Who briefs the board. Who logs the decisions. IR-OS lets you command and run the room with confidence: faster cadence in the moment, smaller blast radius at the end, a tamper-evident record after. Built for the organizations that have outgrown improvisation.
✓ Five-minute setup · ✓ No sales call · ✓ Public pricing · ✓ 30-day money-back guarantee
Cryptographic chain of decisions
Every decision lands on a hash-anchored ledger. Independently verifiable. The audit substrate of the whole platform, not a feature bolted on.
Seven named operator agents, bounded scope
Containment, Comms, Compliance, Insurance, Forensics, Recovery, Lessons. The room runs on agents, not on heroes. Every action they take is traceable to a decision and to a person.
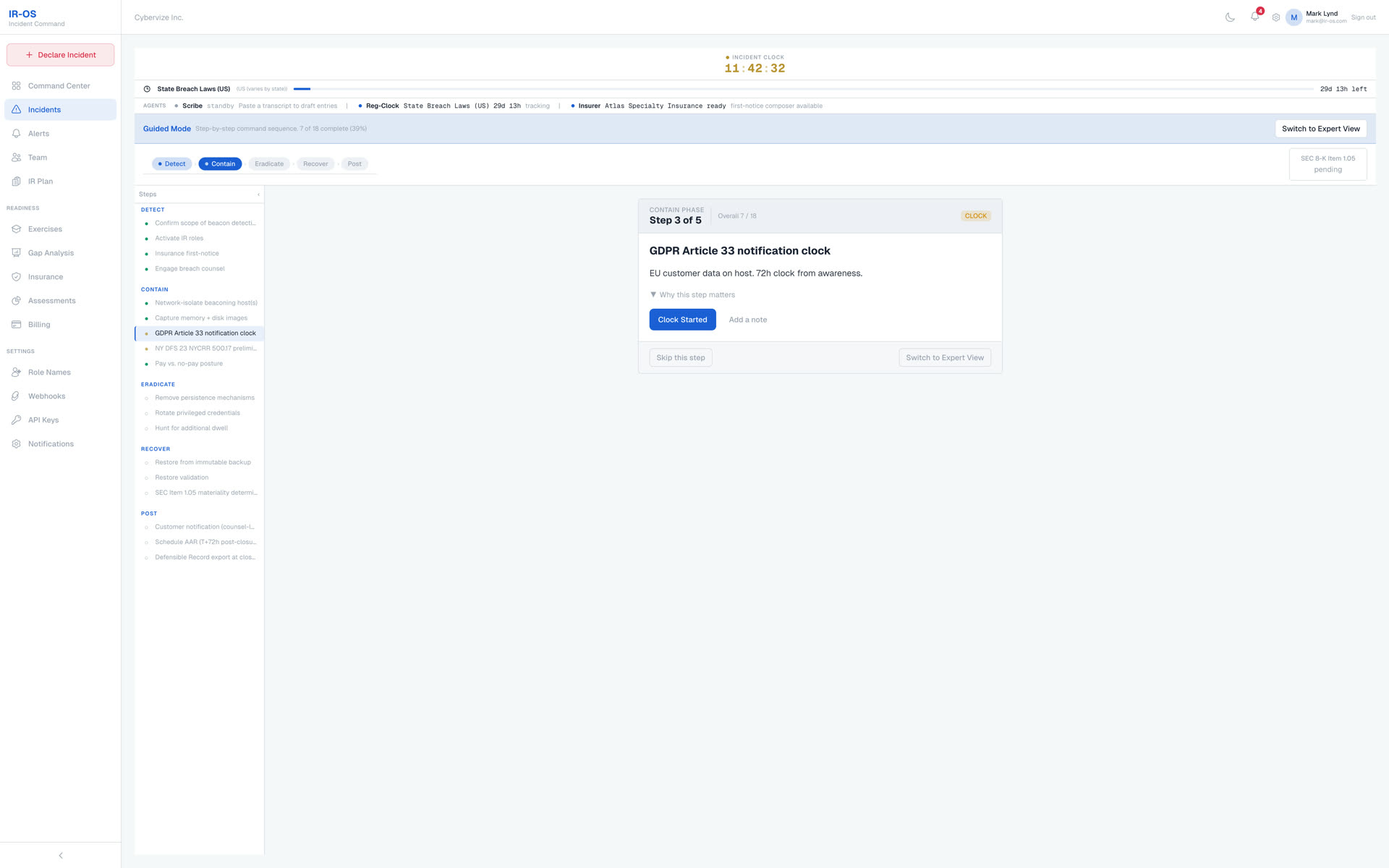
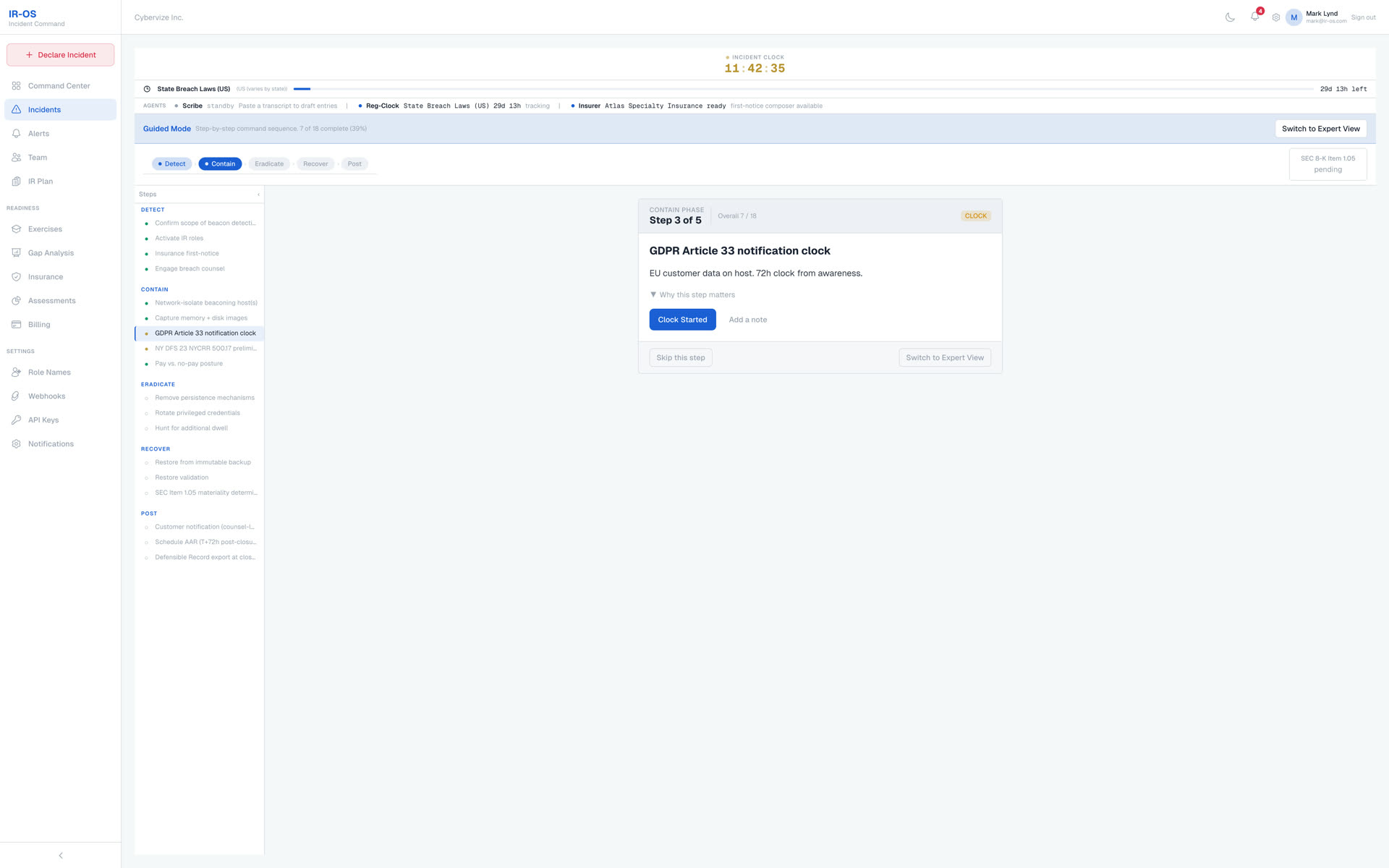
Regulatory clocks built in
SEC Item 1.05 (4 business days), GDPR Article 33 (72 hours), NIS2, DORA, HIPAA, state breach laws. Auto-tracked from the moment materiality is asserted, not when someone remembers.
Featured in and recognized by
Ten findings from 150+ C-suite cyber tabletop exercises facilitated across 32 industries. The coordination, communication, and regulatory failures that no post-incident report surfaces because they get fixed before the report is written.
Free · No email required · Cited by CISOs, security journalists, and IR consultancies
Most organizations do not lose incident-response cases because they failed to detect the breach. They lose because the response was uncoordinated, out of order, and under-documented while it was happening.
People under pressure do not know what their role requires at this exact phase, who owns the next decision, or what document governs it. The documents that actually matter, the IR plan, the cyber policy, regulatory cheat sheets, crisis comms templates, panel-firm contacts, are scattered across SharePoint, an attorney's inbox, somebody's laptop, and a binder in a drawer. Most are PDFs nobody has opened in eighteen months.
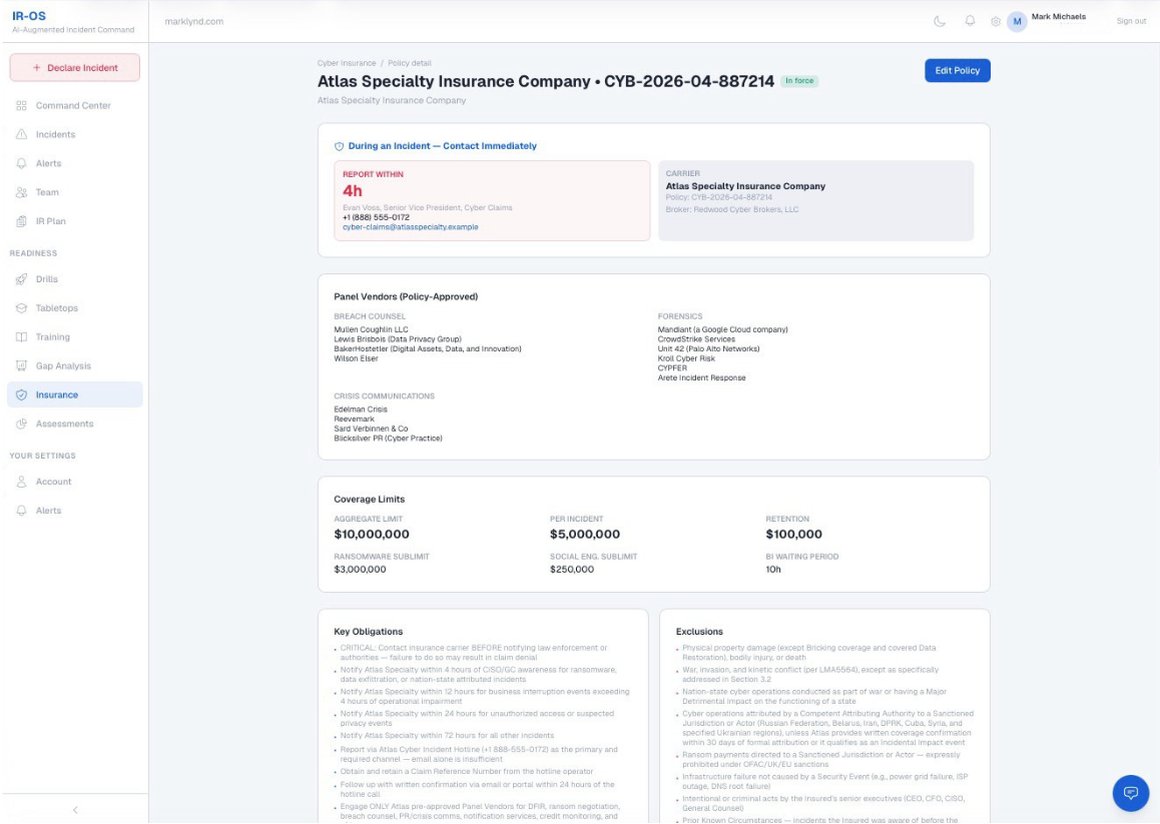
The CFO and General Counsel hold the cyber insurance policy. The CISO and IT report the incident to the FBI in the first hour, which feels right and earns instinctive trust. Twenty-four hours later the carrier denies the claim, because the policy required first-notice to the carrier before any law-enforcement contact, and nobody on the response side knew that clause existed.
Multiply that one missed clause by dozens of regulatory clocks, eight role assignments, twelve crisis comms templates, and four panel firms running at the same time, under sleep deprivation and pressure. That is the problem.
Every minute spent uncoordinated is another minute the attacker keeps moving. Slower response means a larger blast radius. Larger blast radius means more customers in scope, more regulators in scope, more cost. Pace is not a process metric. It is a balance-sheet metric.
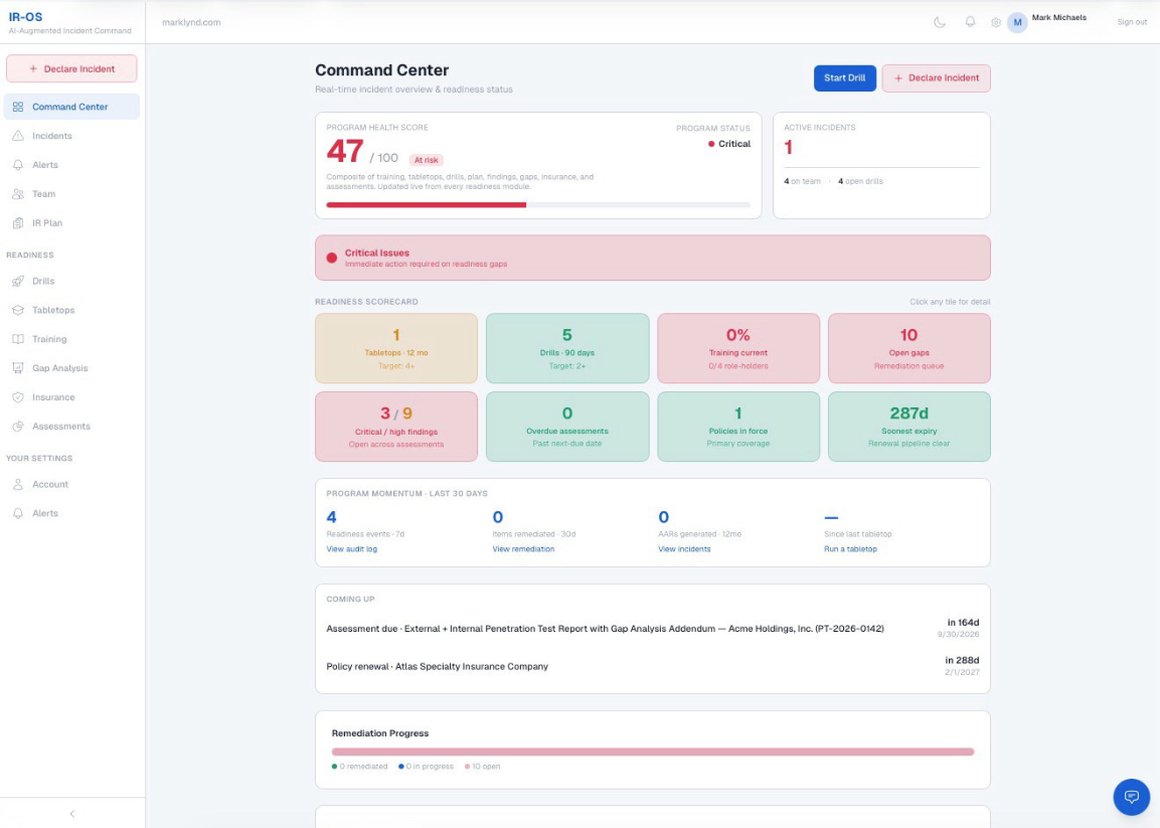
TL;DR: IR-OS is a Cyber Incident Response Management (CIRM) platform that coordinates the human side of cyber incident response - roles, decisions, regulatory clocks, stakeholder communications, and a cryptographically defensible record. Every workflow is built for the audiences a cyber incident actually has. Our Advisory Board includes Mark Lynd, who has facilitated 150+ C-suite tabletops across his career.
IR-OS complements detection tools like SIEM and EDR. Where those answer “what is happening?”, IR-OS answers “who decides, when, and how do we prove it?” It is built on frameworks including NIST SP 800-61 and aligned to regulatory regimes including GDPR Article 33's 72-hour clock, HIPAA, state breach laws, and cyber insurance first-notice windows.
Key Takeaway: According to the Verizon Data Breach Investigations Report and the IBM Cost of a Data Breach analysis, most breach cost is concentrated in containment time which is a coordination problem, not a detection problem. IR-OS closes that gap. Read our data-backed coordination gap analysis, the 2026 incident response playbook, or our ransomware response guide.
Three outcomes, in order: faster cadence in the moment, smaller blast radius at the end, a tamper-evident record after.
Guided steps know the phase. Tasks know the owner. Documents know the moment they belong to. Nobody is reading a 50-item runbook trying to find their place at 3am.
Regulatory clocks, panel firms, and insurance attestations surface at the right moment. Less missed scope, less after-the-fact notification spend, lower fine bracket.
Every event is hash-chained and Ed25519-signed at closure. Anyone can verify the bundle at app.ir-os.com/verify, no account needed. Built for regulators, insurers, and opposing counsel.
Five-minute setup · No sales call
23 attorney-shape templates. Privilege chain. Hash-chained signoffs. Watermarked sample exports. You author it. You send it from your own domain. IR-OS never touches delivery.
Holding statements, customer breach letters, regulator notifications (SEC 8-K, GDPR Article 33, HIPAA HHS, NY DFS, state AG), public statements, internal updates, board briefs. Each cited to the rule it satisfies.
Every signoff captures a sha256 of the exact wording approved. Privileged drafts marked structurally so they do not bleed into the disclosable record.
Sample templates carry a diagonal SAMPLE watermark. Once you clone and edit into your library, the watermark drops. Every export is logged on the chain - hand a regulator the PDF and the /verify URL.
Your DKIM, your reputation, your legal recipient list. We hand you the document. You and your counsel decide who gets it and when.
Card required, cancel anytime before day 7 · 30-day money-back guarantee
Ask AI is a domain-trained assistant and expert coach that helps you configure your plan, optimize readiness, and act during incidents - with cited answers grounded in your IR plan, your incidents, your insurance policy, and the regulatory standards that apply to your organization.
Helps you set up roles, runbooks, and tabletops the first time, spots readiness gaps day-to-day, and answers "what do I do next" with citations during a real incident.
Already knows your active incidents, IR plan, tabletops, gap analysis, and cyber insurance policy. No copy-paste. No re-explaining your environment.
Grounded in NIST 800-61, ISO 27035, CISA, MITRE ATT&CK + D3FEND, OFAC, EDPB, FBI IC3, and 150+ real tabletop patterns. Live web search for today's CVEs and advisories, scoped to cyber and IR.
Engages on incident response, compliance, BCP, security budgeting, vendor selection, board communication, and the current threat landscape. Not a general-purpose chatbot.
Card required, cancel anytime before day 7 · 30-day money-back guarantee · No installation, no consulting
Most IR tools assume you already have a plan, a team, a practiced routine, and a process. IR-OS assumes you don't, it gets you there, then keeps you sharp.
Conversational AI interview asks about your industry, regulators, team, and stack. Generates a plan mapped to NIST 800-61 or ISO 27035.
For each of the six IRC functions, AI recommends the job title in a typical organization that owns it (General Counsel for Legal Liaison, VP Comms for Crisis Communications, Security Engineering Lead for Technical Lead). You name the actual person. We never ingest your org chart.
Run quarterly tabletops on real scenarios. AI facilitates, captures findings, tracks gaps. Every exercise builds your readiness baseline, so when a real incident hits, you're not starting from zero.
Real-time clocks. Hash-chained record. AI copilot. Board briefing ready. Every action logged. Every regulator covered.
30-day money-back guarantee
This is what AI is supposed to deliver, and it's the biggest gap most organizations still struggle to close. Incident response is where that gap hurts most: understaffed teams, regulatory clocks that don't stop, and boardroom stakes on every decision.
IR-OS closes the gap by handing AI the work that used to steal your people's hours, so your team ships board-grade, regulator-ready outcomes on the first pass.
IR-OS doesn't just activate during an incident. Five managed AI agents run continuously on your behalf, monitoring readiness, watching incidents, facilitating exercises, scanning threats, and building your private knowledge base. No other CIRM platform has agents that think about your organization when you're not.
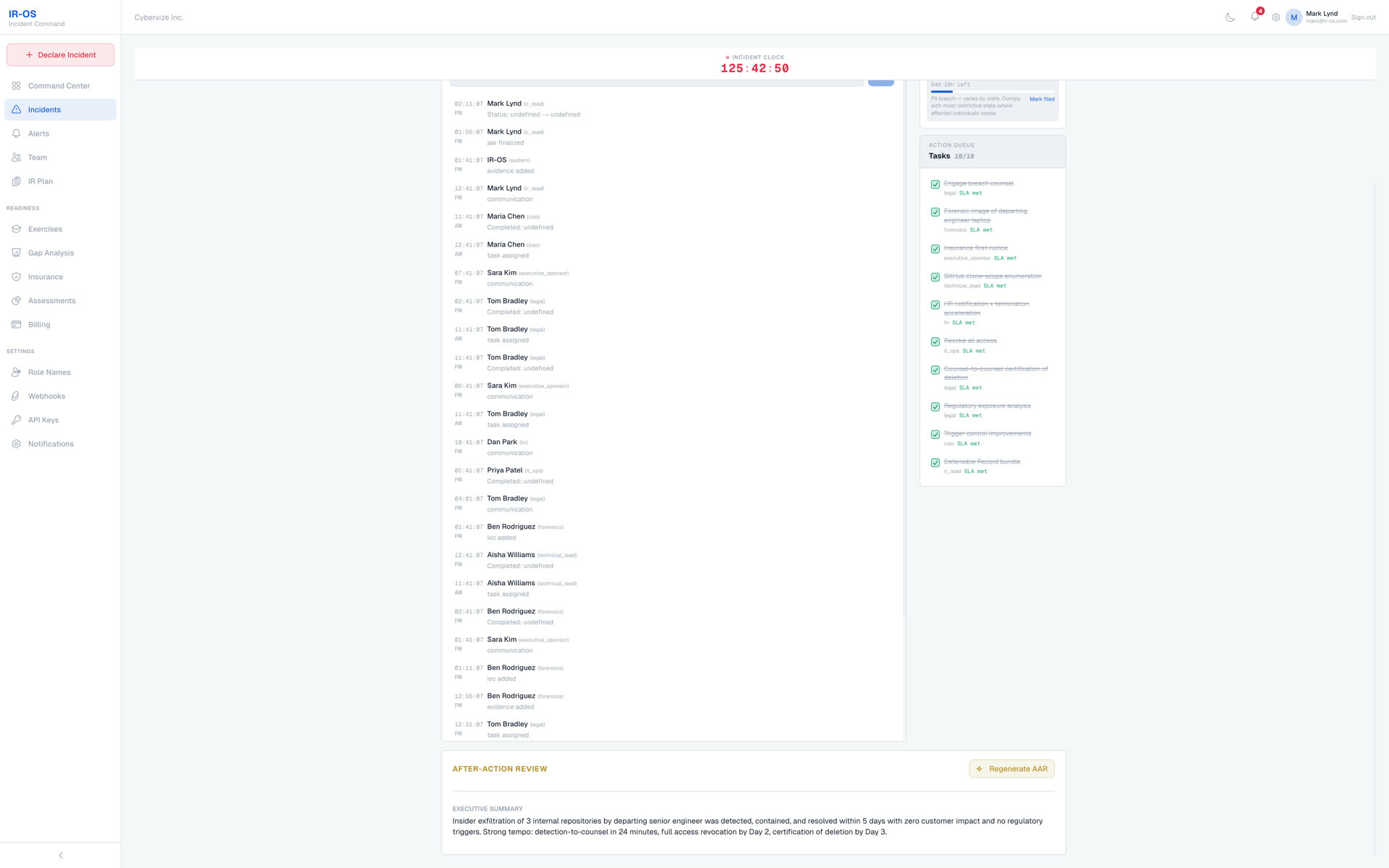
When you close an incident, this agent automatically generates a board-ready Word document, an Excel gap analysis, and a PDF defensible record, with web-searched CVE context and hash-chained proof.
Tier: Command + Theater
A built-in war room where every responder sees the same live feed and @AI is always in the room. Watches the event stream, flags regulatory deadlines, and delivers board briefs, regulatory notices, or threat assessments on demand, cited and seconds away.
Tier: Command + Theater
An AI facilitator trained on the patterns surfaced in 150+ real C-suite tabletops our Advisory Board has facilitated. Presents scenarios, delivers timed injects, probes weak decisions, and generates the exercise AAR with gap tracker items. Self-serve tabletops at scale.
Tier: Theater · Powered by Claude Opus
Runs weekly. Assesses your readiness posture (plan staleness, exercise compliance, insurance expiry, open gaps) and cross-references CISA advisories and MITRE ATT&CK updates against your specific environment.
Tier: Command (monthly) · Theater (weekly)
Upload your own AARs, IR plans, tabletop records, and policies. This agent processes them into structured, retrievable chunks that every other agent can cite, your private institutional memory, searchable by AI.
Tier: Theater
Every agent action is recorded in the SHA-256 hash-chained event ledger. AI suggestions require human approval. The agents advise your team decides. The record proves exactly what the AI recommended and when.
All tiers · FRE 901 ready
The competitive moat: these agents require a structured event ledger, a RAG knowledge base, deep tenant context, and a reasoning model capable of synthesizing across all of them. Most competitors have zero of these. IR-OS has all five.
Three distinct readiness surfaces, each with its own defensible record. Every module attested, every drill scored, every tabletop findings-tracked. All rolled into one tamper-evident readiness trail a regulator, insurer, or board member can inspect on demand.
Ten role-aware modules covering the NIST lifecycle, IR roles, regulatory clocks, containment vs. evidence, breach counsel, ransom decisions, after-action discipline, and the IR-OS platform. Every completion is legally attested with IP and user-agent captured, then hash-chained into the audit log. Re-attestation required every 365 days.
Was: Annual "click through" e-learning Now: Defensible per-member proof
Five to ten minute scenario drills any team member can run anytime. Seven threat archetypes: ransomware, data breach, BEC, insider threat, supply chain, phishing, DDoS. AI judges each decision as best, acceptable, suboptimal, or wrong, then produces an after-action report automatically. Per-member drill history and decision-quality trendlines roll up to the Readiness dashboard.
Was: One tabletop a year, unscored Now: Weekly drills, AI-scored
Formal sixty-to-one-hundred-twenty minute tabletop exercises for the whole command team, facilitated by an AI trained on the operational patterns from the 150+ exec tabletops Mark Lynd has facilitated across his career. Every finding becomes a tracked remediation item with an owner and deadline. Produces the exact record your regulator, auditor, or insurance carrier asks for.
Was: Lost PowerPoints and no follow-up Now: Tracked findings, owners, deadlines
One readiness trail
Every module completion, every drill score, every tabletop finding is hash-chained into the same tamper-evident audit log as your live incident timelines. When a regulator, board member, or cyber insurer asks "prove you were ready," you hand them a cryptographically verifiable record instead of a PowerPoint.
From minute 0 through Day 90. Where the time, the money, and the senior-team attention actually go.
See the timeline comparison →7-day free trial · 30-day money-back guarantee
Regulators want evidence. Insurers want proof. Plaintiffs want gaps. IR-OS gives you an append-only, hash-chained incident record that proves exactly what happened, when, and who decided.
Append-only, events can never be edited or deleted after creation
SHA-256 hash chain, each event cryptographically links to the previous one
Exportable, full timeline available for legal, regulatory, and insurance review
150+ executive cyber incident response tabletops across Fortune 500s, critical infrastructure, and the public sector, with one consistent verdict on what IR-OS gets right.
“I've run more than 150 executive cyber incident response tabletops across Fortune 500s, critical infrastructure, and the public sector. The same three failures show up every time. Coordination breaks down. Nobody can prove what was decided and when. And the after-action work never actually updates the plan. IR-OS is the first platform I've seen that fixes all three by construction, not by process discipline. Its AI-native design (cited answers on every page, a grounded IR Brain, native MCP integration) compounds on itself. Organizations that adopt it don't just respond faster. They do more with fewer responders and deliver exponentially better outcomes on every incident. That is the actual promise of AI, and one of the biggest gaps most organizations still face. IR-OS is the first platform I've seen that keeps that promise for incident command.”
Different decision-makers, different value. Pick yours.
The answer to "what now" is already on screen. State plus role equals view. Your responders see only what they need to do next, not a fifty-item runbook.
Less time in the war room. Faster recovery to production. One platform where IT, security, legal, comms, and the business see the same state and the same next action, so coordination does not collapse into Slack threads. A defensible record you can hand to the CEO, the board, and the audit committee without rebuilding it from email after the fact.
Regulatory clocks tracked from your policy text. A defensible record that survives discovery. Refuse-to-build list keeps governance theater out of the platform.
Shorter incidents. Lower notification spend. Lower fine bracket. Cleaner insurance recovery. Pace becomes dollars saved on every event.
SOC 2, pen tests, insurance attestation, tabletops, and the after-action review with linked remediation, all on one audit-ready substrate.
The screen tells the team what to do next so you can think two steps ahead. Forgiving for edits, confirmed for destruction. Voice and keyboard input, both audited.
Five-minute setup · No sales call
Customer names and organizations are intentionally anonymized. Strong cyber-hygiene, the same kind we teach in our tabletops, means not exposing your incident-response stack to anyone profiling your defenses.
"When my team opens the dashboard we know who owns what, which clocks would start, and what counsel would need to see. That kind of confidence is hard to put a price on, and it is what we did not have before."
Marcus T., Chief Information Security Officer
Mid-market Financial Services Organization
"My responsibility is making sure the record we keep would hold up if anyone ever asked. With IR-OS I can answer that question honestly. The artifact is exportable, the privilege model is real, and that is what lets me sleep."
Helen K., General Counsel
Regional Healthcare System
"Cyber insurance was the line item I worried about most. The first-notice workflow is wired to our policy trigger, the documentation writes itself, and our broker now uses our setup as a reference example. That is the value I was looking for."
Priya S., Chief Financial Officer
Growth-stage SaaS Company
"Our drills used to be a calendar invite people dreaded. We are more than 5x as ready as we were before, practicing on the same surface we would actually use, and nobody has to ask where to look. That is the difference between knowing a plan and being able to run one."
David R., Director of Incident Response
National Retail Chain
"Communications used to be our slowest workstream because every draft needed three approvals routed by email. The signoff trail captures all of that natively, drafts stay under privilege, and my team can move at the pace the moment requires."
Yvonne L., Vice President of Communications
Multinational Manufacturer
"My board chair stopped asking for ad-hoc updates because the briefing she needs is one click away. The audit committee conversation changed character entirely. We are governing the program now, not reacting to it."
Anita J., Chief Executive Officer
PE-backed Industrial Services Firm
"For an organization our size, the value is that we look prepared without pretending to be something we are not. The plan is real, the drills are real, and the record is real. That is the whole point of readiness."
Brent M., Chief Information Security Officer
State-level Public-Sector Agency
Procurement teams don't lose sleep over marketing claims, they lose sleep over audit reports. Here's the shared-responsibility reality of IR-OS: what we inherit from our providers, and what we own in our own code.
Your organization's data is cryptographically isolated at the database layer. Every query is bound to the caller's tenant before a single row returns. Cross-tenant reads are not possible by construction, not by convention.
A cryptographic audit trail records every material governance event, training, drills, account changes, settings changes. Integrity can be mathematically verified; modification after the fact is detectable.
Integration keys are single-purpose by design, a key issued for one surface cannot reach another. Keys are stored only in hashed form, minted with strong entropy, visible to you once, and revocable in a single click.
Short-lived authenticated sessions, modern password requirements, re-authentication for sensitive operations, and multi-factor authentication support. Privileged actions are server-gated before the page renders.
Multiple independent layers protect every request, network edge, browser hardening, abuse protection, and runtime scope enforcement. No single control is the only thing standing between an attacker and your data.
Every AI surface is advisory-only. Context is scoped to your own organization. Answers are grounded in cited sources, no fabrications, no cross-tenant exposure, no ability for the AI to modify platform state.
Detailed security documentation available to prospects under NDA hello@ir-os.com
IR-OS plans, runbooks, and the audit trail are built on recognized cyber-IR standards. Pick the framework your program runs on. We carry the rest.
Plus a Standards Watcher Agent on the roadmap that monitors NIST, ISO, CISA, MITRE, OASIS, OFAC, SEC, EDPB, and FBI IC3 daily, then drafts plan amendments with citations the moment something material changes.
Your IR program stops drifting the moment it is signed.
Three plans. Every plan includes the defensible record, the IR Brain, and every AI capability. Pick the one that matches your team size and complexity, not a segment. Federal, SLED, and enterprise teams can procure on your paper via verified POs and standard contract vehicles, see the procurement options.
All plans include a 7-day free trial and a 30-day money-back
guarantee. Card required up front, cancel anytime before day 7.
Are you a first responder, fire, EMS, or law enforcement
agency?
You may qualify for discounted pricing
contact us
and we'll take care of you. Also, state/local government, K-12, and
higher ed is available upon request, you must
reach out to us.
Federal agencies, state and local government, K-12, higher ed, and enterprise teams can procure IR-OS through standard procurement instruments. We accept verified purchase orders and common federal and SLED procurement paperwork, including:
Submit the form below with your procurement details. We review every submission personally, verify the instrument, and respond within two business days with next steps, required documentation, and a point of contact for the rest of the process.
Everything you need to know about IR-OS and incident command.
ir-os-mcp package is a standalone MCP server
that runs locally (via npx) and talks to IR-OS over
HTTPS with a scoped, revocable mcp:read API key you
mint from Settings → API Keys. Six read-only
tools are exposed in v0.1: list incidents, get timeline, compute
regulatory clocks, list panel vendors, read plan phase, and
search the IR Brain RAG. Write tools (declare incident, append
timeline entry) require a separate mcp:write scope
that's on the Phase 2 roadmap with explicit audit-log integration.
Still evaluating options? Compare IR-OS side-by-side.
Cytactic · BreachRx · Cydarm · ServiceNow SIR · FireHydrant · PagerDuty · incident.io · spreadsheets
See every comparison →Every Friday afternoon ends someone's quarter. Every unpatched server is a ticking audit trail. Have an IR plan, command team, and defensible timeline ready in 15 minutes, not 15 months.
Full platform access. Cancel in one click.